OSI model
OSI model (Open Systems Interconnection Reference Model – another name - ISO OSI RM, sometimes called ISO/OSI) is a model of network communication structure, formulated by ISO organization. It is a reference model for most communication protocols families.
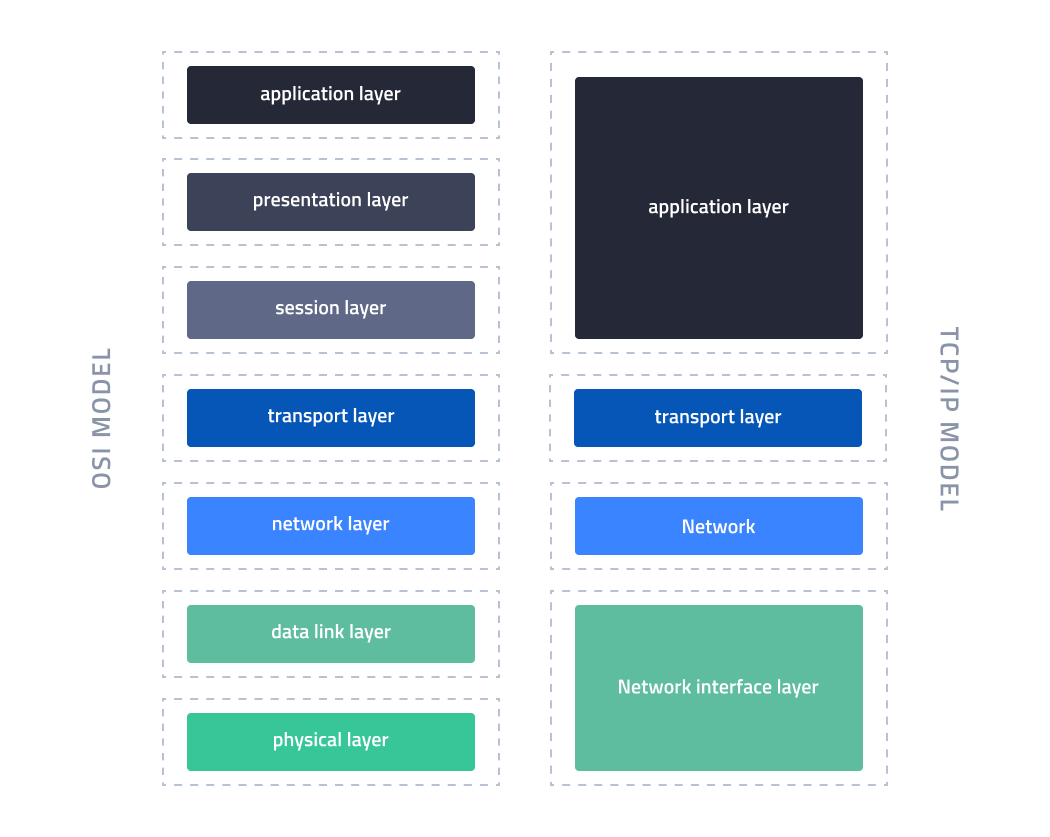
In the case of the Internet, a simplified model is used - the TCP/IP model.
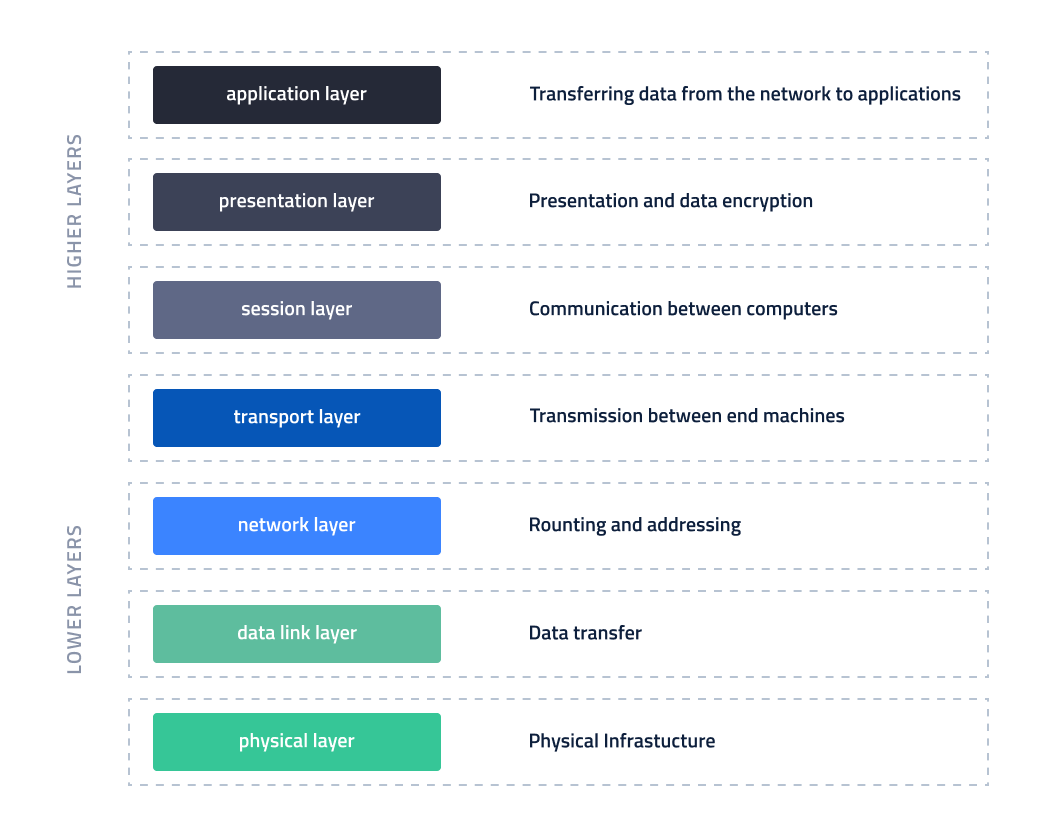
OSI model is made of seven layers, which describe the course of communication between two devices. This model describes both electric impulses of the lowest layer, as well as displaying data by the highest one.
TCP and OSI models can be called "protocol stacks": they are made of many layers, each operating under specified rules and protocols. The term "protocol stack layer" addresses communication models.
If you've read about DoS and DDoS attacks, you've probably noticed references to the third, fourth, and/or seventh layer. It was the OSI model that was referenced in such cases.
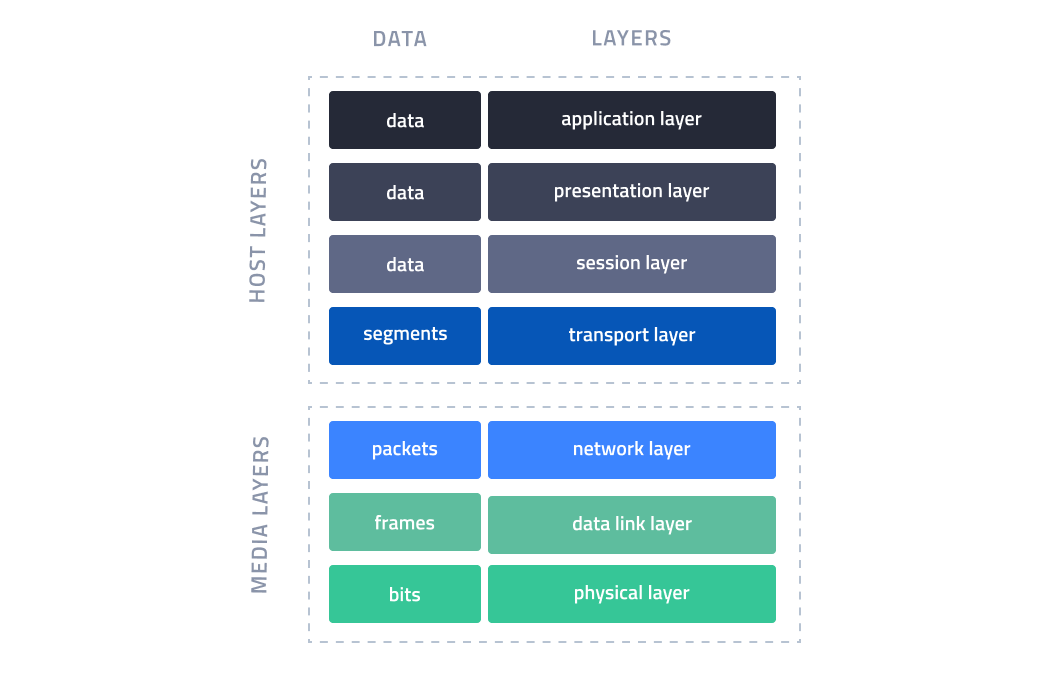
As data is transferred down from highest to lowest layers, it is encapsulated - it is sent with a new header, compatible with the layer it is in. In turn, when it is received and goes up from the lowest layers to the highest ones, it is decapsulated.
In the next part of this article, each layer will be described, starting with the lowest ones.
1. Physical Layer
The lowest layer is the physical structure of the network, responsible for transferring information from one node to another - in the form of electric, radio, or optical signals. It defines, among others, electric voltage levels, pace and maximum distances of data transferring, and also types of cables or frequencies in case of wireless communications.
In this layer, data is transmitted in its simplest form - bits, or zeros and ones.
2. Data link layer
This layer physically addresses machines, for example using MAC addresses (MAC address - individual address of network card). It also oversees the physical layer and ensures high quality of information transported in it, also changing its parameters if needed. It specifies protocols used for the initiation/termination of communication and data transfer.
In this layer, information is packaged in frames and sent/received in this form.
3. Network layer
This layer contains information on network infrastructure and is responsible for choosing routes - including routing between separate networks - in which packets between sender and receiver will be transferred.
The base packet sent in this layer is NDPU, Network Protocol Data Unit, which does not contain any information important for the user. Instead, it is used for establishing a connection between two machines. In this layer, the IP protocol is used - IPv4 and IPv6.
The information transmitted in this layer is called packets.
4. Transport layer
The fourth layer, the transport layer, uses protocols to stabilize and carry out the connection between two machines. It ensures services like:
data transfer control and reliability,
communication-oriented connection,
multiplexing.
Communication is performed with protocols, with the most popular being Transmission Control Protocol. TCP requires mutual confirmation of communication.
Another protocol is a simpler one, the UDP - User Datagram Protocol. It is used for faster packet transfer and unlike TCP, does not require mutual confirmation. Because of that, it is useful in amplificated DDoS attacks, as data sent does not have to be accepted by the receiver. You'll learn more about DDoS attacks here.
The transport layer sends data divided into segments.
You can read more about DDoS attacks here.
5. Session layer
The session layer controls sessions between devices - it establishes the connection, manages, and terminates it. It also provides authorization services, session control and restoring. In TCP/IP model, it is split between transport, and application layer, and its tasks are performed by the TCP protocol. In this layer and higher ones, data is sent.
In this and higher layers, data is transmitted.
6. Presentation layer
The presentation layer ensures that data sent is correctly understood by both machines, guaranteeing context between various systems and networks (i.e. it guarantees correct sending and reading of media files, like PNG, so both computers understand it correctly).
It passes requests from the application layer to the session layer. Data encoding and decoding usually take place in this layer (for example, connections with banks are encrypted).
7. Application layer
The last, highest layer is the closest one to the user and it contains applications working on the machine.
TCP/IP highest layer is also called the application layer, however, it has more functionality than in OSI RM (it contains, for example, communication protocols).
OSI model in practice
Depending on the device, packets going through it may be limited to lower layers. For example, switches and repeaters operate only on the physical layer, and routers in the physical, data link, and network layer.
Differences between OSI and TCP/IP
TCP/IP model is much simpler than the OSI model and it has only four layers. However, despite completely different premises, their layers can be compared.
The two lowest layers of the OSI model correspond to a single, lowest layer of TCP/IP model - network access layer. The Internet layer of TCP corresponds to the network layer; both of those models have a transport layer, the one in TCP/IP also has a part of OSI's session layer. The rest of the session layer, presentation layer, and application layer of the OSI model are all contained in a single layer of TCP/IP model, also called the application layer.